Insight Health
How the way you walk tells the story of your health – Aidan Boran and Gaitkeeper


Engage with Insight - work with one of Europe's largest data science centres

Insight is hiring! Check out our jobs page


Latest News
Get our latest news in your inbox
Sign up for the Insight newsletter!
Insight in Numbers
0
+
Researchers
€ 0
+
Million in Funding
0
+
Industry Partners
0
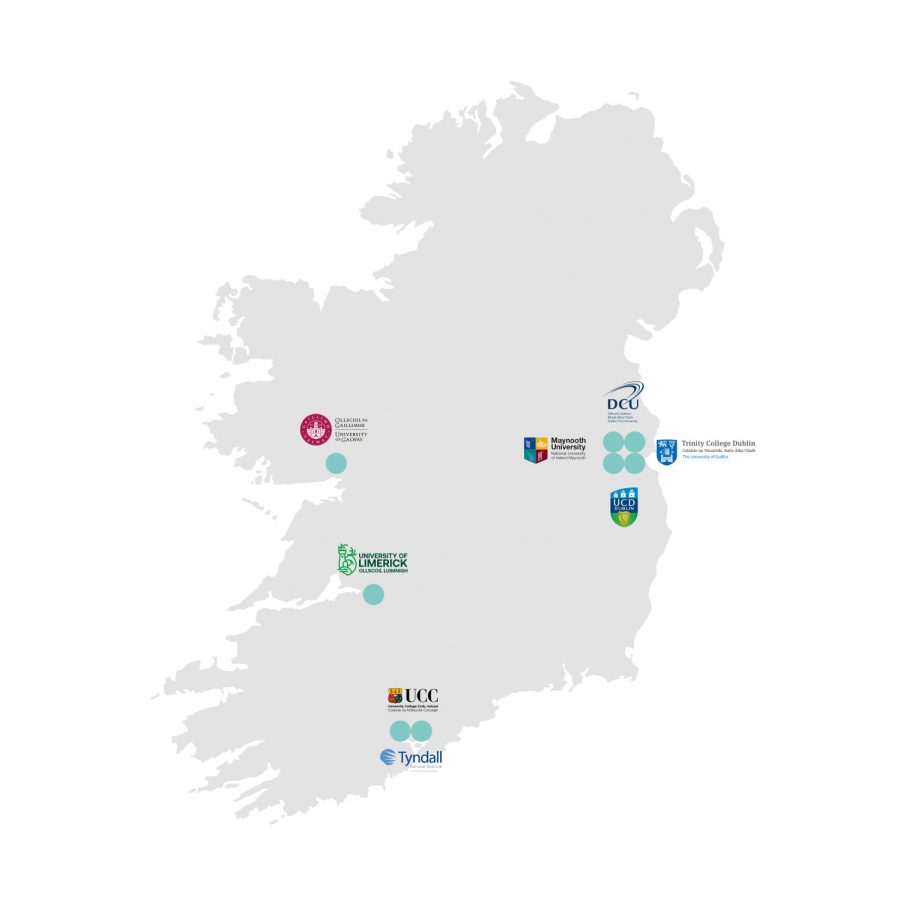
Research Institutions

